You might have heard about this old adage - "boot access==root access". It is indeed true! Any one who can access the boot loader can easily get the root access to your system. We already have posted a guide that described how to reset root password in Linux. That tutorial taught you how to easily reset or recover root user password via Grub bootloader. Once someone has physical and/or bootloader access to a machine, there is no way to stop them. That's why we need to add an extra security by protecting the Grub Bootloader with a strong password. If you're a Linux administrator, you should know how to secure your bootloader. This guide explains how to protect Grub bootloader with password in CentOS. I tested this guide on CentOS 6.x and CentOS 7.x systems and it worked just fine as described below.
Password Protect GRUB Bootloader in RHEL 6.x, CentOS 6.x
In older Linux distributions like CentOS 6.x, RHEL 6.x, Grub is the default bootloader. This section describes how to set grub password in CentOS 6.x systems.
Before doing any changes, it is always recommended to backup the GRUB configuration file
# cp /etc/grub.conf /etc/grub.conf.bak
First, we need to encrypt the password. To do so, log in to your centos system as root user and create a file named grub as shown below. All commands given below should be executed as root user.
# touch grub
Next, encrypt the password using "md5crypt" command. To do so, run the following command from the Terminal and press ENTER key.
# grub-md5-crypt >grub
Enter your password twice. Please note that you won’t see anything as you type the password on your screen. Just type the password anyway and press ENTER, and re-type the same password and press ENTER.
The password has been encrypted. Next, we need to add this password in /etc/grub.conf file.
Now, let us add the password in the grub.conf file. To do so, open the two files grub and /etc/grub.conf files.
# vi /root/grub /etc/grub.conf
The above command will open the both files in vi editor.
You will see the encrypted password like below. Move the cursor point and place it in-front of the password. Then, type yy to yank (copy) the password.
Password: Retype password: $1$Ch0NF/$0XsWw8.EW31vRjm5zsnPb/
And then, type :n (colon n). This will switch you to the next file i.e /etc/grub.conf.
After the splashimage=(hd0,0)/grub/splash.xpm.gz line, press p to paste the encrypted password from the previous file.
Then, press i and add the line password --md5 before the encrypted password as shown below.
password --md5 $1$I2w2s1$EPZtrLn/h2M4qfh48ZL8O0
Refer the following screenshot for more clarification.
Here, $1$I2w2s1$EPZtrLn/h2M4qfh48ZL8O0 is my CentOS 6 system's encrypted grub password. Replace it with your own.
Then, press ESC and type :wq to save the file and close it.
Reboot your system.
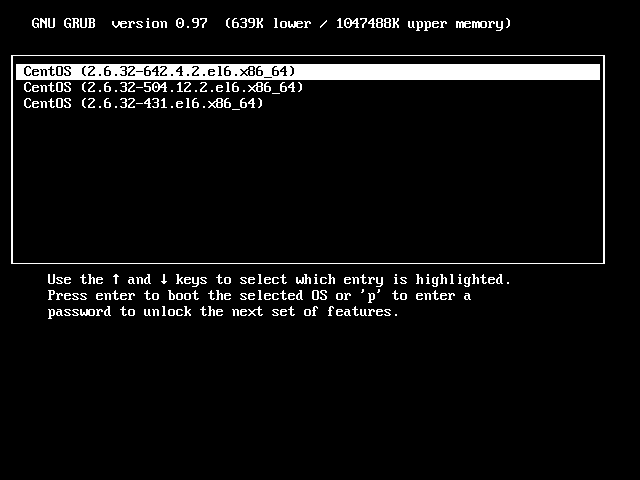
From now on, you can’t edit grub menu without entering the password first.
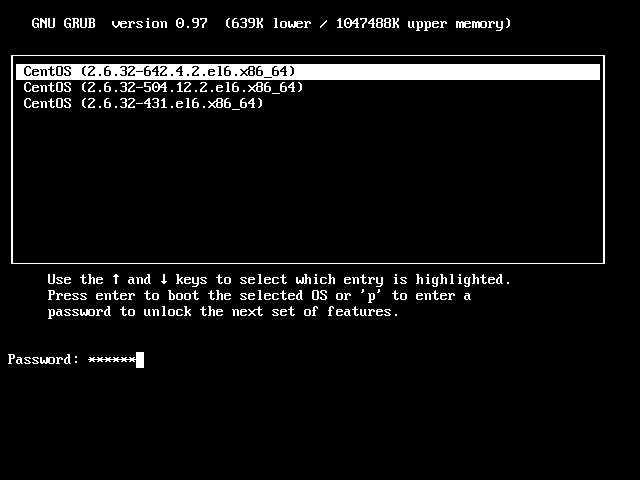
To edit the Grub menu, press p. You will be asked to enter the password. Just enter the password to unlock the Grub boot menu.
Now, you can make any changes you want in the grub boot menu.
Password Protect GRUB2 Bootloader in RHEL 7.x, CentOS 7.x
In RHEL 7 and its clones like CentOS 7, Scientific Linux 7, Grub2 is the default bootloader. Protecting Grub2 bootloader with password is different than grub bootloader.
First, create the encrypted password using the following command as root user:
# grub2-mkpasswd-pbkdf2
Sample output:
Enter password: Reenter password: PBKDF2 hash of your password is grub.pbkdf2.sha512.10000.62C46DE64C6BDE39A440092F521F86E24F486F5F9FE58B38D1CA9DDA27D6DDA6A6F5615836537B31AF2D06D2C5A8C6BE26709269A08E81286357501882016523.FD91A05503B0538FBA4CF9783A13727C43917E63528FF9FFC9917E4780B9C420CEDAE98451CF9256BA77AC144FA6734CA193D1E4183AC71E1F297BD7868FFC4B
We have just created an encrypted password to secure the Grub2 bootloader.
As you might already know, It is not recommended to edit and paste the newly generated password directly in the grub2 main configuration file.
Instead, we should add the password in a custom Grub2 menu file which is found in /etc/grub.d/ directory, and finally update the Grub2 main configuration file i.e /etc/grub.cfg.
Make a copy of the custom Grub2 menu file:
# cp /etc/grub.d/40_custom /etc/grub.d/40_custom.bak
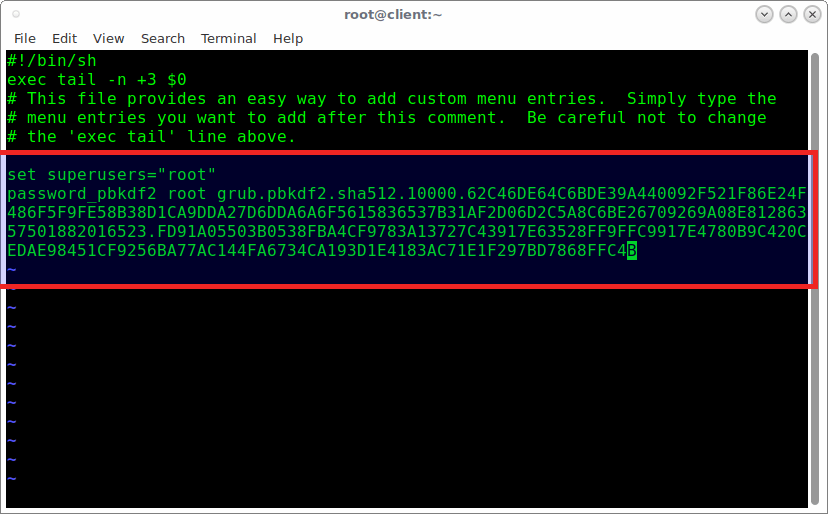
Then, Edit the custom Grub2 menu config file as root user:
# vi /etc/grub.d/40_custom
Add the following lines. Make sure you have pasted the correct password which we generated earlier.
set superusers="root" password_pbkdf2 root grub.pbkdf2.sha512.10000.62C46DE64C6BDE39A440092F521F86E24F486F5F9FE58B38D1CA9DDA27D6DDA6A6F5615836537B31AF2D06D2C5A8C6BE26709269A08E81286357501882016523.FD91A05503B0538FBA4CF9783A13727C43917E63528FF9FFC9917E4780B9C420CEDAE98451CF9256BA77AC144FA6734CA193D1E4183AC71E1F297BD7868FFC4B
Press ESC and type :wq to save and close the file.
Now, it is time to update the Grub2 main configuration file.
Make sure you have backup copy of the Grub2 main config file.
# cp /boot/grub2/grub.cfg /boot/grub2/grub.cfg.bak
Update Grub2 bootloader configuration file using command:
# grub2-mkconfig -o /boot/grub2/grub.cfg
Sample output:
Generating grub configuration file ... Found linux image: /boot/vmlinuz-3.10.0-327.22.2.el7.x86_64 Found initrd image: /boot/initramfs-3.10.0-327.22.2.el7.x86_64.img Found linux image: /boot/vmlinuz-3.10.0-327.13.1.el7.x86_64 Found initrd image: /boot/initramfs-3.10.0-327.13.1.el7.x86_64.img Found linux image: /boot/vmlinuz-3.10.0-123.9.3.el7.x86_64 Found initrd image: /boot/initramfs-3.10.0-123.9.3.el7.x86_64.img Found linux image: /boot/vmlinuz-3.10.0-123.el7.x86_64 Found initrd image: /boot/initramfs-3.10.0-123.el7.x86_64.img Found linux image: /boot/vmlinuz-0-rescue-e250d471d5594282ba042c653cfa0172 Found initrd image: /boot/initramfs-0-rescue-e250d471d5594282ba042c653cfa0172.img done
You can verify if the password has been set correctly in the /etc/grub2.cfg file as shown below.
# cat /etc/grub2.cfg
Sample output would be:
We're all set. Reboot your system to verify if the bootloader has been secured with password.
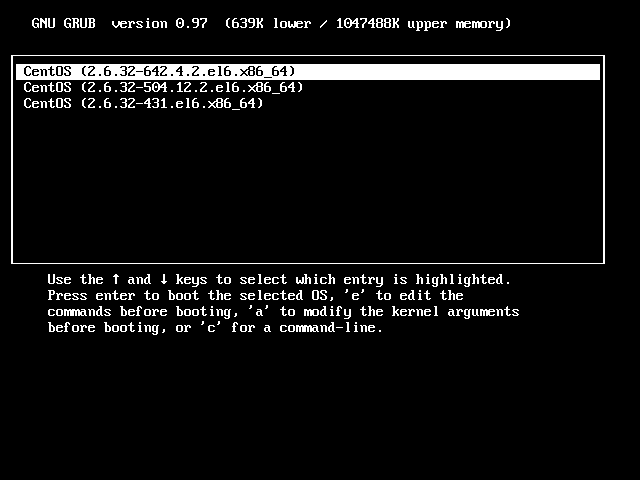
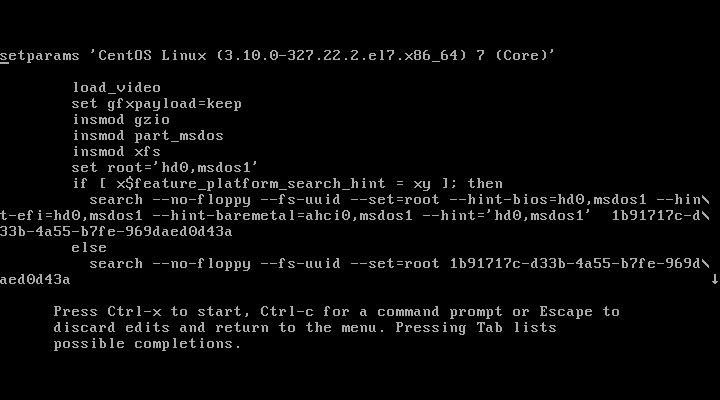
After restarting the system, try to edit Grub2 bootloader. To do so, press e.
You'll be asked to enter the user name and password which we have defined in the earlier step.
If you entered the correct username and password, you'll be able to edit the Grub2 bootloader.
You know now how to password protect the Grub and Grub2 bootloader in Linux. Setting Grub password may not completely protect your system. However, it will definitely add an extra security layer to your CentOS Linux servers.







7 comments
Very informative and useful article!
Thank you !!
I’ll try to figure out how to do it on an Arch system.
Glad to know that I helped you. Cheers!
On my system you have to be root to edit the grub.cfg file, so I’m not sure what this adds to the situation.
And what if you boot from a USB stick, or CD / DVD? And thus bypassing GRUB?
Can’t you access all files then? Can’t you even reinstall GRUB then?
The only way to prevent acces I can think of, is encrypting the root file system (or at least /home)
Am I wrong?
You’re right. I didn’t say protecting GRUB alone will protect your system. There are other ways too. I will posting more guides related to Linux security.
Hi,
If You are using multi-boot system You have to make some addition to „30_os-prober” as well. Otherwise any alien software will be locked with newly created password. At least that’s the Fedora 28/grub2 case.
Any first level menu should contain one more parameter: „–unrestricted”.
E.g.:
The original line:
menuentry ‘$(echo “${LONGNAME} $onstr” | grub_quote)’ $CLASS –class os \$menuentry_id_option
The edited line:
menuentry ‘$(echo “${LONGNAME} $onstr” | grub_quote)’ $CLASS –class os –unrestricted \$menuentry_id_option
Thank you very much for the tip. Hope this will be helpful for someone who use dual boot.