The su command is a powerful tool that can be used to switch to another user's account. However, it can also be used by bad persons to gain unauthorized access to your system. By restricting the use of the su command, you can help to protect your Linux system from unauthorized access.
Table of Contents
Introduction
In our previous tutorial, we learned how to "grant or deny sudo access to a group" in Linux to make things safer and manage groups better. However, this alone may not be enough.
If a bad person gains access to an account without sudo privileges, they can still try to login as root or another user with sudo privileges by using the su command. As you already know, the su command allows users to execute commands as other accounts, including the root account.
To address this concern, we need to ensure that only specific accounts have the privilege to use the su command. This extra step will add even more security to our system. In this brief tutorial, we will learn how to restrict the su command usage to authorized users in Linux.
Here are some of the reasons why you might want to restrict the use of the su command:
- To prevent unauthorized users from gaining access to sensitive data.
- To prevent unauthorized users from making changes to system settings.
- To prevent unauthorized users from installing malicious software.
1. Restrict Su Command Usage to Particular Users in Debian and its Derivatives
To limit who can use su command, we need to create a dedicated group and allow only the members of that particular group can use su command. Let us see how to do that.
1. For the purpose of this guide, I am going to create two users namely user1 and user2.
$ sudo adduser user1
$ sudo adduser user2
2. Next, create a new group called adminmembers.
$ sudo groupadd adminmembers
3. Add the 'user1' and 'user2' to the group.
$ sudo usermod -aG adminmembers user1
$ sudo usermod -aG adminmembers user2
Similarly, add all other users to this group.
You can verify the members of this group using command:
$ getent group adminmembers
Sample output:
adminmembers:x:1005:user1,user2
4. Now, run the following command to restrict the su command to only the members of the 'adminmembers' group:
$ sudo dpkg-statoverride --update --add root adminmembers 4750 /bin/su
Here, the sudo dpkg-statoverride --update --add command is used to override file permissions and ownership for a specific file on a Debian-based Linux distribution. In this case, the command is setting a special permission and ownership for the /bin/su binary.
Let's break down the command:
sudo: This is used to run the command with superuser (root) privileges. You will need administrative privileges to modify system files.dpkg-statoverride: This is a command-line tool in Debian-based systems that allows you to override file permissions and ownership of packages managed by the package manager.--update: This option tellsdpkg-statoverrideto update the specified override if it already exists.--add: This option indicates that we want to add a new override.root: This specifies the user whose ownership will be set for the file.adminmembers: This specifies the group whose ownership will be set for the file.4750: This is the numeric representation of the file permissions. The value4750is a special permission called "SetUID" (Set User ID) on execution. When thesubinary has the SetUID bit set, it runs with the effective user ID of the file owner (root) instead of the user who executed it. This allows regular users to switch to the root user's privileges temporarily when runningsu./bin/su: This is the path to the file for which the override is being set. In this case, it's the/bin/subinary, which allows users to switch to another user's account (often the root user) after providing the necessary password.
So, the command is adding an override for the permissions and ownership of the /bin/su binary. It sets the file's owner to root, group to adminmembers, and gives the SetUID permission to the file. This means that when users run the su command, it will run with root privileges, allowing them to switch to the root user or another user with superuser privileges after providing the appropriate password. The non-members of the 'adminmembers' group can't use su command, even if they have sudo privilege.
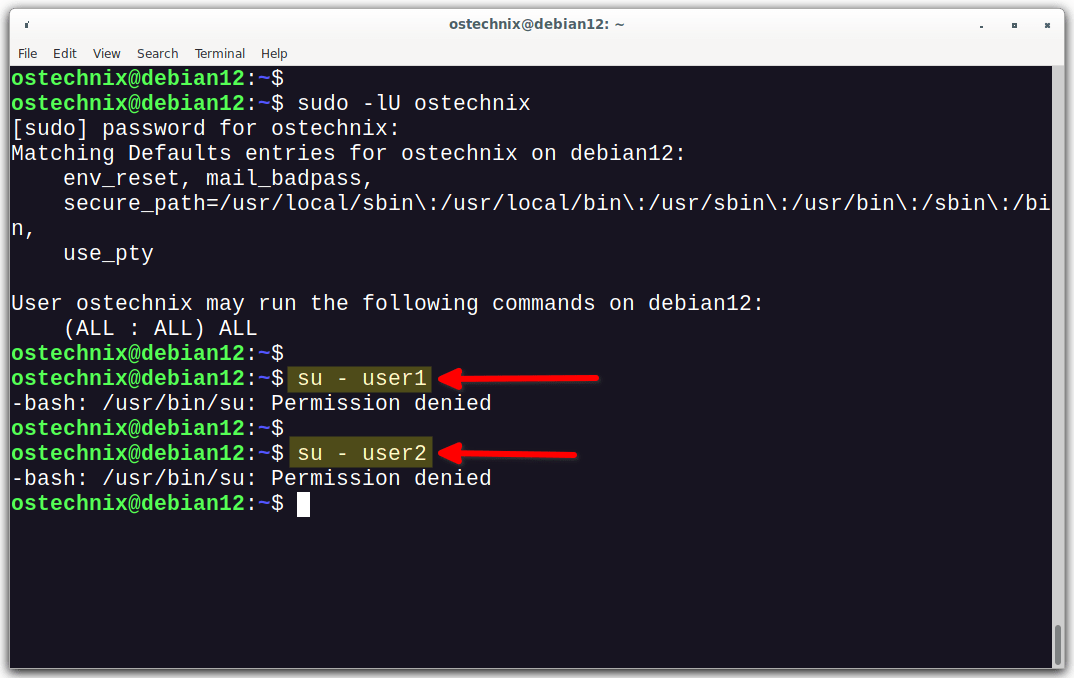
Let us verify it. Right now, I'm logged into my system as a user named 'ostechnix', and this user has sudo privileges.
$ sudo -lU ostechnix
[sudo] password for ostechnix:
Matching Defaults entries for ostechnix on debian12:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
use_pty
User ostechnix may run the following commands on debian12:
(ALL : ALL) ALLAs you see in the above output, the user 'ostechnix' can able to run all commands.
Now, let use su command and see what happens.
$ su - user1
Sample output:
-bash: /usr/bin/su: Permission denied
See? The user 'ostechnix' can't use the su command despite having sudo privilege because he is not a member of the 'adminmembers' group. Because, we limited the su command usage to only the members of that specific group.
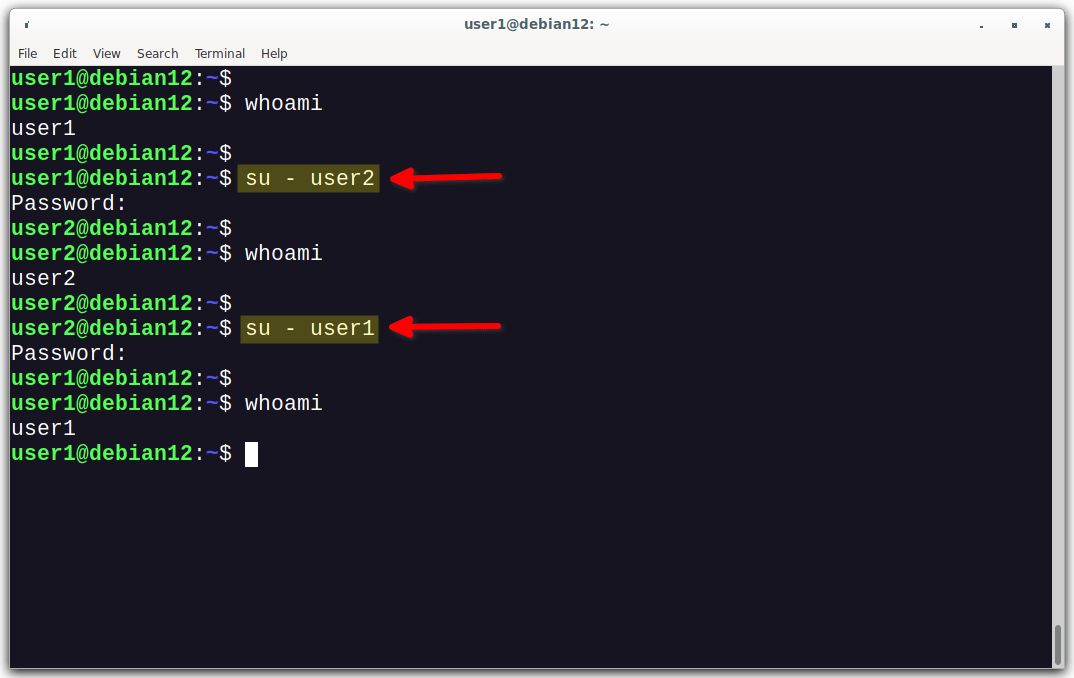
Now log out from the current session and log back in as 'user1' or 'user2' or any member of the 'adminmembers' group.
And, check if su command works:
user1@debian12:~$ whoami user1 user1@debian12:~$ user1@debian12:~$ su - user2 Password: user2@debian12:~$ user2@debian12:~$ whoami user2 user2@debian12:~$ user2@debian12:~$ su - user1 Password: user1@debian12:~$ user1@debian12:~$ whoami user1 user1@debian12:~$
As you can observe in the above output, both 'user1' and 'user2' have the ability to switch between different user accounts using the su command because they are both members of the 'adminmembers' group.
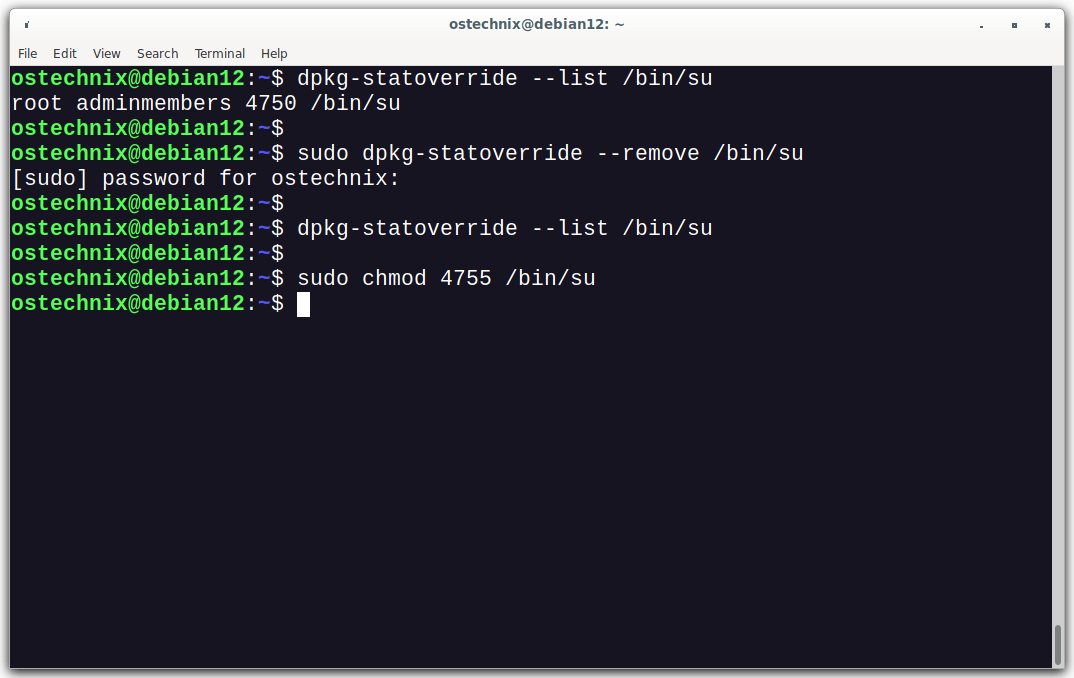
1.1. Revert su Command to its Original Configuration
To undo the changes made by the command sudo dpkg-statoverride --update --add root adminmembers 4750 /bin/su, you need to remove the override that was set for the /bin/su binary. The dpkg-statoverride command allows you to manage file permissions and ownership for packages in Debian-based systems.
To remove the override for the /bin/su binary, follow these steps:
1. Check the current dpkg-statoverride configuration:
Before removing the override, it's a good idea to check if the override for /bin/su exists and what the current configuration is. Run the following command to view the current dpkg-statoverride settings:
$ dpkg-statoverride --list /bin/su
This command will show you the current permissions and ownership set for the /bin/su binary.
Sample output:
root adminmembers 4750 /bin/su
2. Remove the dpkg-statoverride entry:
To remove the override, use the following command:
$ sudo dpkg-statoverride --remove /bin/su
This command will remove the override entry for /bin/su.
3. Reset the original permissions (if needed):
If you want to reset the permissions of /bin/su to the default value, use the following command:
$ sudo chmod 4755 /bin/su
The 4755 value sets the SetUID bit on the file, which allows the su command to run with root privileges.
With these steps, you should have undone the changes made by the initial sudo dpkg-statoverride --update --add root adminmembers 4750 /bin/su command and reverted the /bin/su binary to its original configuration.
Warning: Always exercise caution when modifying system configurations, especially when dealing with file permissions and ownership, as improper changes can impact system security and stability.
2. Limit the Use of Su Command in RHEL-based Systems
The previous method is only for Debian and its derivatives like Ubuntu. The process of limiting su command usage in RPM-based is different. Let us see how to do that.
To limit the use of the su command in RHEL-based systems, follow these steps:
1. Create a new user (e.g., "user1") and add him to the "wheel" group:
$ sudo adduser user1
$ sudo passwd user1
$ sudo usermod -G wheel user1
This grants the user "user1" access to the su command through the "wheel" group, which is often configured to have special privileges.
2. Open the PAM configuration file for su using a text editor:
$ sudo nano /etc/pam.d/su
3. Append the following line at the end of the file or uncomment this line if it already exists:
auth required /lib/security/pam_wheel.so use_uid
Alternatively, you can uncomment or append this line:
auth required pam_wheel.so use_uid
4. Save the changes and close the file.
With these steps, the su command will be restricted, and only users belonging to the "wheel" group will be allowed to use it.
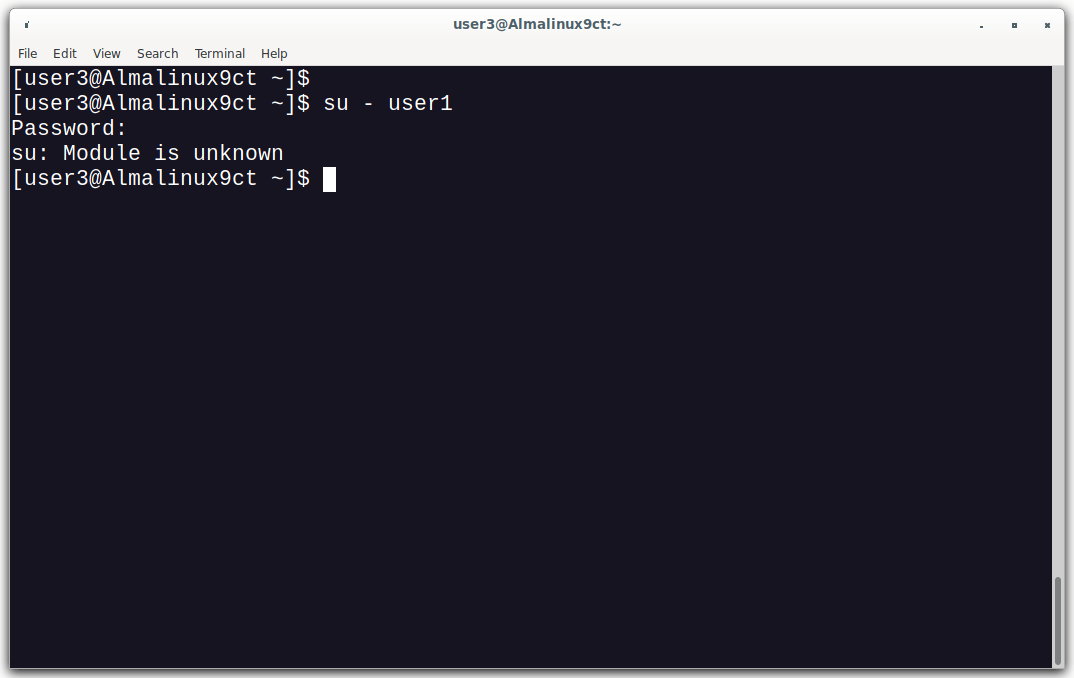
When you try to use su command from a non-member of wheel group, you would see an output like below:
[user3@Almalinux9ct ~]$ su - user1 Password: su: Module is unknown
To revert back to the original settings, simply comment or remove the line that you've added in the previous step.
Frequently Asked Questions
su command in Linux?A: The su command, short for "switch user," allows users to execute commands as a different user, often the root user with superuser privileges.
su command usage?A: Restricting su command usage enhances security by limiting access to privileged operations, reducing the risk of unauthorized users gaining unrestricted control over the system.
su command?A: You can limit su command usage by configuring the PAM (Pluggable Authentication Modules) file, allowing access only to specific groups or users, such as the "wheel" group.
su for a specific group?A: Add the desired users to a designated group (e.g., "wheel") and configure the /etc/pam.d/su file to require this group membership for su command access.
su command is appropriately restricted?A: Use the su command with a non-privileged user to verify that access is limited only to authorized users or groups.
Conclusion
Restricting the usage of the su command in Linux is a vital step towards strengthening Linux system security and safeguarding sensitive information. By carefully controlling access to privileged commands, such as su, we can mitigate the risk of unauthorized users gaining elevated privileges and potentially compromising the system.
Implementing these restrictions, in conjunction with other security best practices, creates a more resilient and secure Linux environment.
Related Read: