There are many popular remote desktop sharing programs (such as Teamviewer, Guacamole, and TigerVNC etc.) you can use when you need to share your screen to your co-workers or friends. These programs will share your entire screen to others. But, if you want to share only the Terminal, you can just use Tmate. It is actually a fork of Tmux, a terminal multiplexer that lets you to use several programs in a single Terminal. They both can be installed on the same system at the same time. Tmate is something like a Teamviewer for your Terminal.
For those wondering, Tmate will establish a secure connection over SSH to tmate.io website and generate a random URL for each session. You can share the URL with someone you trust and they can use the Terminal as the way they use their own Terminal as long as the connection is active. It is best for collaborating on common projects, or debugging a project with a team of developers, or getting a technical support over remote network. Tmate supports all popular operating systems, including GNU/Linux, Mac OS X, and BSD systems.
In this tutorial, I will explain how to install and use Tmate in Unix-like operating systems.
Table of Contents
Installing Tmate in Linux
For Arch Linux, and its derivatives like Antergos, Manjaro Linux, Tmate is available in AUR, so you can install it using AUR helper programs such as Yay.
$ yay -S tmate
For Fedora, run the following command to install Tmate.
$ sudo dnf install tmate
On Ubuntu, and its derivatives like Linux Mint, you can install in using the following PPA.
$ sudo apt-get install software-properties-common $ sudo add-apt-repository ppa:tmate.io/archive $ sudo apt-get update $ sudo apt-get install tmate
On Ubuntu 18.04 LTS versions, enable the universe repository and install Tmate like below.
$ sudo add-apt-repository universe
$ sudo apt install tmate
On FreeBSD:
# pkg install tmate
OpenBSD:
# pkg_add tmate
Configure SSH
Before start using Tmate, we need to create a SSH key-pair. Because, the tmate program establishes a secure SSH connection with tmate.io using the local SSH key pair.
Let us create SSH key-pair using command:
$ ssh-keygen -t rsa Generating public/private rsa key pair. Enter file in which to save the key (/home/sk/.ssh/id_rsa): Created directory '/home/sk/.ssh'. Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/sk/.ssh/id_rsa. Your public key has been saved in /home/sk/.ssh/id_rsa.pub. The key fingerprint is: SHA256:DL3+rYrYtXYHxyFfDSRAsz4470wAQ+V/iW+sd5/fnA0 sk@ubuntuserver The key's randomart image is: +---[RSA 2048]----+ | ....+.... | | . o o .. | | + o . o | | = =..... .| | S =+oo | | . +.=+ | | o oo+ E | | o o.*.+o .o=| | . o.oo*+.. +B| +----[SHA256]-----+
If you don't create, you will see the following notification message at the bottom of the Terminal window.
[Tmate] Reconnecting... (SSH keys not found. Run 'ssh-keygen' to create keys and try again.)
Share Your Terminal Instantly using Tmate
Once you created the SSH key-pair, launch Tmate by running the following command from your Terminal:
$ tmate
If you entered a passphrase while creatingSSH keypair, you may need to enter it to establish the Tmate session.
After you started the Tmate session, share the connection ID with anybody you want to share your screen with. You can share it with any number of people you trust. They need not to be in the same network or need not to use the same OS. They don’t even have to have tmate or tmux installed.
This is how Tmate sessions looks like.
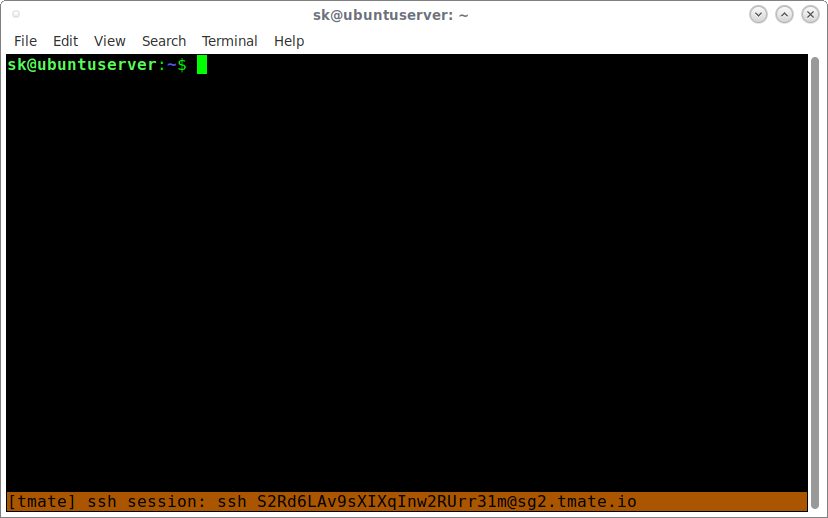
As you see in the above screenshot, there is a SSH session ID (a string of random characters) at the bottom of the screen. Just copy and share it with others to connect. Please note that this ID will disappear after a few seconds. However, you still can view the sessions IDs using command:
$ tmate show-messages
Sample output would be:
Fri Aug 11 17:18:48 2017 [tmate] Connecting to ssh.tmate.io... Fri Aug 11 17:18:49 2017 [tmate] Note: clear your terminal before sharing readonly access Fri Aug 11 17:18:49 2017 [tmate] web session read only: https://tmate.io/t/ro-UVgrzHg2BVanPXZnt6JtlpU3V Fri Aug 11 17:18:49 2017 [tmate] ssh session read only: ssh ro-s8EGu5v1WessJXBuUj7SR2adg@sg2.tmate.io Fri Aug 11 17:18:49 2017 [tmate] web session: https://tmate.io/t/LVWgMSX2wNhBLdrLfxtcX00rk Fri Aug 11 17:18:49 2017 [tmate] ssh session: ssh S2Rd6LAv9sXIXqInw2RUrr31m@sg2.tmate.io
As you see in the above output, you can either share the Terminal via SSH session or a web session using the respective session IDs. You can also share either the read-only session or read-write session.
Very Very important note: Please be mindful that if you have given read-write session IDs (either SSH or Web), the user can do anything. Because, you just gave him your system access with sudo rights. So, I strongly suggest you to give read-only session IDs.
When you're sharing the read-only session, you don't want to let the remote users to view the other read-write session IDs. So, just clear the Terminal before giving the session IDs to the users.
Connect via SSH sessions
For those who wants to share the Terminal via SSH sessions, give the SSH session ID to the remote users.
For example, the remote users to enter the following command to access read-only Tmate session from their system.
$ ssh ro-s8EGu5v1WessJXBuUj7SR2adg@sg2.tmate.io
In the read-only session, the remote users only can view your Terminal. They can't run any commands.
To share the read-write session, the command is:
$ ssh S2Rd6LAv9sXIXqInw2RUrr31m@sg2.tmate.io
Now, the remote users can access your terminal with as read-write mode. That means they can run any command on your Terminal. All commands they enter in the remote session can also be viewed from your local Terminal.
Connect via Web sessions
For those who wants to share the Terminal via a web browser, just give the web URL to others to connect.
Say for example, to share the read-write, I would give this URL to my coworkers - https://tmate.io/t/LVWgMSX2wNhBLdrLfxtcX00rk
When they enter the above URL, they will see following screen.

Again, I warn you not to give read-write session IDs to anyone unless it is absolutely necessary. Share the read-write sessions with trusted persons only.
Suggested read:
Working under a tmate session is exactly same as tmux. You can think of tmate as a reverse ssh tunnel accessible from anywhere. To exit from a session, type exit. For more details, refer the man pages.
$ man tmate
Resource:
Suggested read:

4 comments
wait… Tmate installs a server?! And this is better than screen why?
Because with screen you can not have someone on another machine view your terminal with you. Tmux and Screen are great tools for when you want to keep your terminals open on a remote machine even after you close the SSH connection, but they are for private use only. This is for when you want to use your terminal collaboratively.
Actually, yes you can. I’ve used it for exactly that purpose that when training people on CLI environments for decades.
See the screen documentation for the multisession and multiuser settings of screen. And screen needs to install no new services or servers.
Frankly, I don’t want people on terminal sessions on my systems if they are NOT actually logged onto the box. At best, it is VERY poor security practice.
Well yes, I know you can do it with screen but it’s a bit more involved and as you said, you need to give people shell access to the machine. That’s not always practical or even possible. Tmate is much easier to use since it’s a simple URL and isn’t blocked when there’s a firewall in the way somewhere, making for a better out of the box experience.
That said, I agree there are some severe security implications. For example, anyone who has write access to the shared terminal can execute the
tmate show-messagescommand, showing all connection URLs for all to see, including users who you only gave the view only URL to. This is an obvious privilege escalation that needs to be addressed.