Installing Docker on Ubuntu is very easy! Anyone, even the newbies, can install it within 15 minutes. After installed Docker, I noticed that I couldn't perform most Docker operations as a normal user. I had to run Docker either as "root" user or with "sudo" permission every time. Whenever I tried to run Docker as non-root user or without sudo permission, I get the following error:
Got permission denied while trying to connect to the Docker daemon socket at unix:///var/run/docker.sock: Get http://%2Fvar%2Frun%2Fdocker.sock/v1.40/version: dial unix /var/run/docker.sock: connect: permission denied
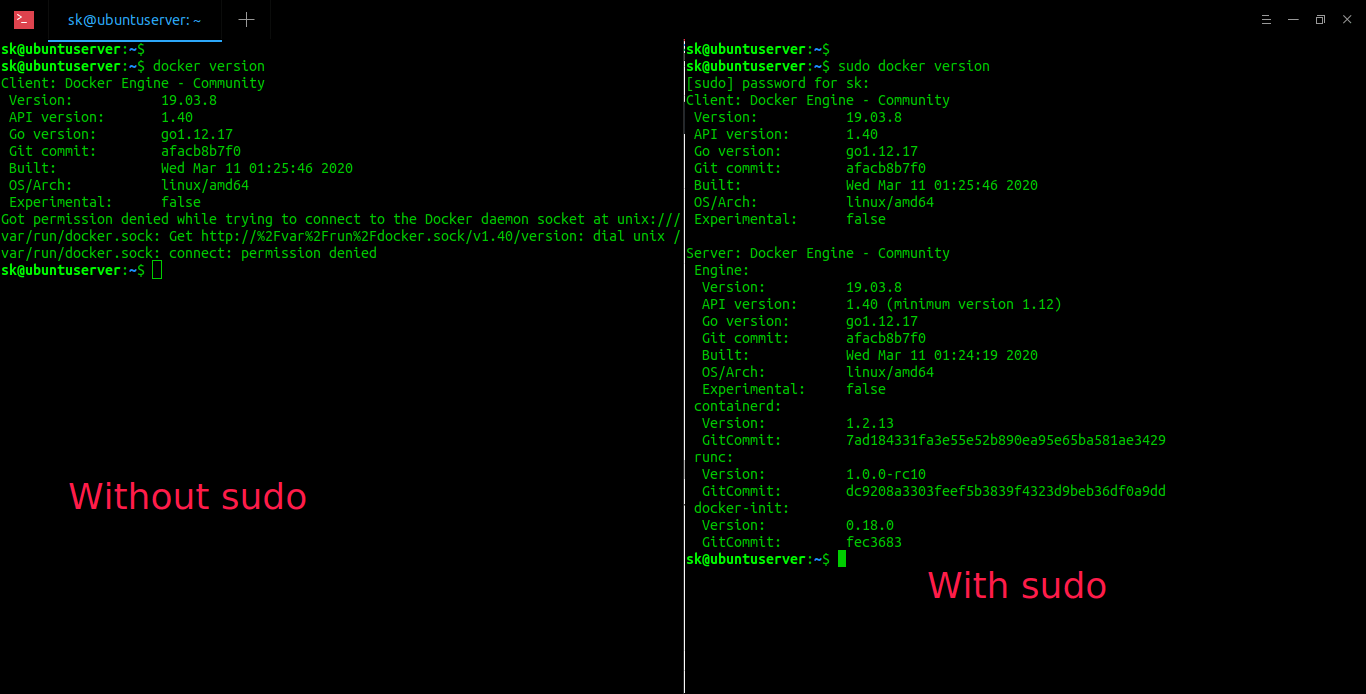
For instance, I wanted to check the Docker version as normal user using command:
docker version
And, I get this error message:
Client: Docker Engine - Community
Version: 19.03.8
API version: 1.40
Go version: go1.12.17
Git commit: afacb8b7f0
Built: Wed Mar 11 01:25:46 2020
OS/Arch: linux/amd64
Experimental: false
Got permission denied while trying to connect to the Docker daemon socket at unix:///var/run/docker.sock: Get http://%2Fvar%2Frun%2Fdocker.sock/v1.40/version: dial unix /var/run/docker.sock: connect: permission deniedBut when I run the same command with sudo permission;
sudo docker version
It displays the whole details of the currently installed Docker version as shown in the below output.
Client: Docker Engine - Community Version: 19.03.8 API version: 1.40 Go version: go1.12.17 Git commit: afacb8b7f0 Built: Wed Mar 11 01:25:46 2020 OS/Arch: linux/amd64 Experimental: false Server: Docker Engine - Community Engine: Version: 19.03.8 API version: 1.40 (minimum version 1.12) Go version: go1.12.17 Git commit: afacb8b7f0 Built: Wed Mar 11 01:24:19 2020 OS/Arch: linux/amd64 Experimental: false containerd: Version: 1.2.13 GitCommit: 7ad184331fa3e55e52b890ea95e65ba581ae3429 runc: Version: 1.0.0-rc10 GitCommit: dc9208a3303feef5b3839f4323d9beb36df0a9dd docker-init: Version: 0.18.0 GitCommit: fec3683
After searching in the Docker documentation page, I realized that the Docker daemon binds to a Unix socket instead of a TCP port by default. Since that Unix socket is owned by the root user, the Docker daemon will only run as the root user. Hence, the normal users can't perform most Docker commands.
If you want to run Docker as non-root user in Linux, you need to do the following steps. I tested this on Ubuntu 18.04 server and it worked just fine! It should also work on other Linux distributions as well.
Important Warning:
Running Docker as regular user is not a good idea for security. I personally do not use this and do not recommend it as well. If it is your personal system and you don't expose your system to Internet, it is not a big deal. However, do not run Docker as non-root user in a production system.
Run Docker as Non-root User in Linux
To fix the Docker permission denied error and use Docker as non-root user, create a group called "docker" with the following command:
sudo groupadd docker
Next, add your user to the docker group:
sudo usermod -aG docker $USER
After adding the user to the docker group, log out and log back in to take effect the changes.
Alternatively, run the following command to apply the changes to groups:
newgrp docker
From now on, the normal (non-root) user can be able to use Docker without sudo permissions.
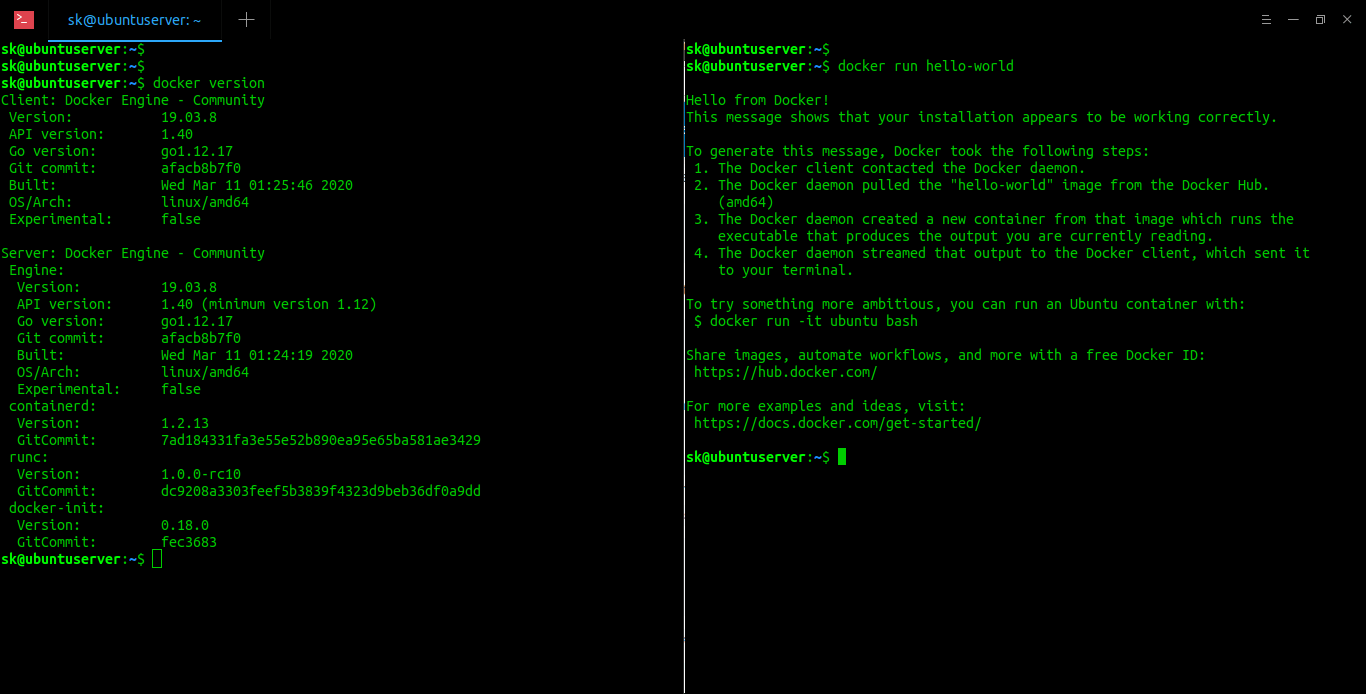
Let me run the following commands as normal user:
docker version
docker run hello-world
Sample output:
See? I can now run those both Docker commands without sudo permission.
Just in case, you already ran a few Docker commands with 'sudo' permission before adding your user to the Docker group, you will probably see an error something like below.
WARNING: Error loading config file: /home/user/.docker/config.json - stat /home/user/.docker/config.json: permission denied
The above error message indicates that your ~/.docker/ directory was created with incorrect permissions due to the 'sudo' commands.
To fix this problem, change this directory ownership and permissions using the following commands:
sudo chown "$USER":"$USER" /home/"$USER"/.docker -R
sudo chmod g+rwx "$HOME/.docker" -R
Log out and log back in for this to take effect.
If it still doesn't fix the issue, you might need to remove your ~/.docker/ directory. It will be recreated automatically, but you will lose all custom settings, if there are any.
Resource:

3 comments
The problem with this is that it can potentially expose your system to root access. Simply run ‘docker run -it -v /:/opt/host debian bash’ and you can read/write to any file as root through /opt/host inside of your docker container. On a personal system, this isn’t too big of a problem, but in a managed user environment where you don’t want users to have root access or access to private information of other users (ssh keys for example), this can be a big issue.
Agreed.
Are there alternatives to a secure user-only docker access without the risk of opening the server to them?