This guide explains a few different ways to find which service is listening on a particular port in Linux. Most of you know the default port of popular services or processes. For example, the default port of Apache is 80, FTP default port is 21 and SSH default port is 22. You can find the port names and numbers in Linux as described in this guide. The default port numbers can also be changed to any custom ports to secure a Linux server. For instance, the following guides describes how to change the defaults port of Apache, FTP and SSH to different port.
- How To Change Apache Default Port To A Custom Port
- How To Change FTP Default Port To A Custom Port
- How To Change SSH Default Port To A Custom Port
If the default port number is changed, how would you find which service is listening on which port? That's what we are going to find out now!
Table of Contents
Find which service is listening on a particular port in Linux
I have listed four methods below to check what service is running in a particular port number. I will keep updating this list if I come across any new methods in future. So, bookmark it and check it once in a while.
Method 1 - Using netstat
This is the most commonly used way to find which service is listening on which port. Netstat is a command line utility used to print network connections, routing tables, interface statistics, masquerade connections, and multicast memberships.
Netstat is available in the default repositories of most Linux distributions.
To install it on Arch Linux and its variants, do:
$ sudo pacman -S net-tools
On Fedora, RHEL, CentOS, AlmaLinux and Rocky Linux:
$ sudo dnf install net-tools
On older RHEL versions and its clones, use yum instead dnf.
$ sudo yum install net-tools
On Debian, Ubuntu:
$ sudo apt install net-tools
After netstat is installed, run the following command to find which services are listening on what ports:
$ sudo netstat -tulpn
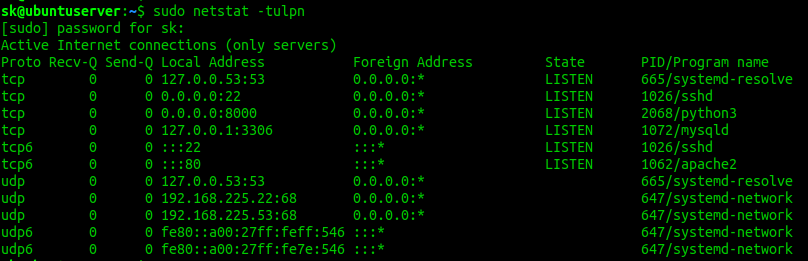
Sample output:
Active Internet connections (only servers) Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 665/systemd-resolve tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 1026/sshd tcp 0 0 0.0.0.0:8000 0.0.0.0:* LISTEN 2068/python3 tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 1072/mysqld tcp6 0 0 :::22 :::* LISTEN 1026/sshd tcp6 0 0 :::80 :::* LISTEN 1062/apache2 udp 0 0 127.0.0.53:53 0.0.0.0:* 665/systemd-resolve udp 0 0 192.168.225.22:68 0.0.0.0:* 647/systemd-network udp 0 0 192.168.225.53:68 0.0.0.0:* 647/systemd-network udp6 0 0 fe80::a00:27ff:feff:546 :::* 647/systemd-network udp6 0 0 fe80::a00:27ff:fe7e:546 :::* 647/systemd-network
As you can see, a python service (simpleHTTPserver in this case) is listening on port number 8000, mysqld service is listening on port 3306, ssh service is running on port number 22, apache2 is running on port 80 and so on.
Here,
-tflag shows tcp connections.-uflag shows udp connections.-lflag displays listening sockets.-pflag displays the process ID(PID) and the process name of whatever is using that port.-nflag displays the numerical addresses.
The above command lists all services and the port numbers they are listening upon. What if you want to find which service is listening on a particular port? Here is where grep command comes in handy! We can combine netstat and grep command to filter the output for a specific service, for example mysqld, like below.
$ sudo netstat -tulpn | grep mysqld [sudo] password for sk: tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 1076/mysqld
See? mysqld service is listening on port number 3306.
If you already know the port number, but don't know which service is currently using it, simply replace the service name with port number as shown below.
$ sudo netstat -tulpn | grep -w 3306 tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 1076/mysqld
Here, -w flag displays only those lines containing matches that form whole words. In other words, -w option shows the exact match of the given string.
You can also use -i to Ignore case distinctions, so that characters that differ only in case match each other
$ sudo netstat -tulpn | grep -i 3306
It is that simple.
For more details, refer man pages.
$ man netstat
Netstat is mostly obsolete. The alternative to netstat is "ss".
Method 2 - Using "ss" command
The netstat command is deprecated in recent Linux versions, so I recommend you to use "ss" instead of netstart.
ss is command line utility to investigate sockets. It is an alternative to netstat and the usage of "ss" is almost same as "netstat". It comes pre-installed on Ubuntu and its variants.
To find which services are listening on which ports, run:
$ sudo ss -tulpn
Sample output:
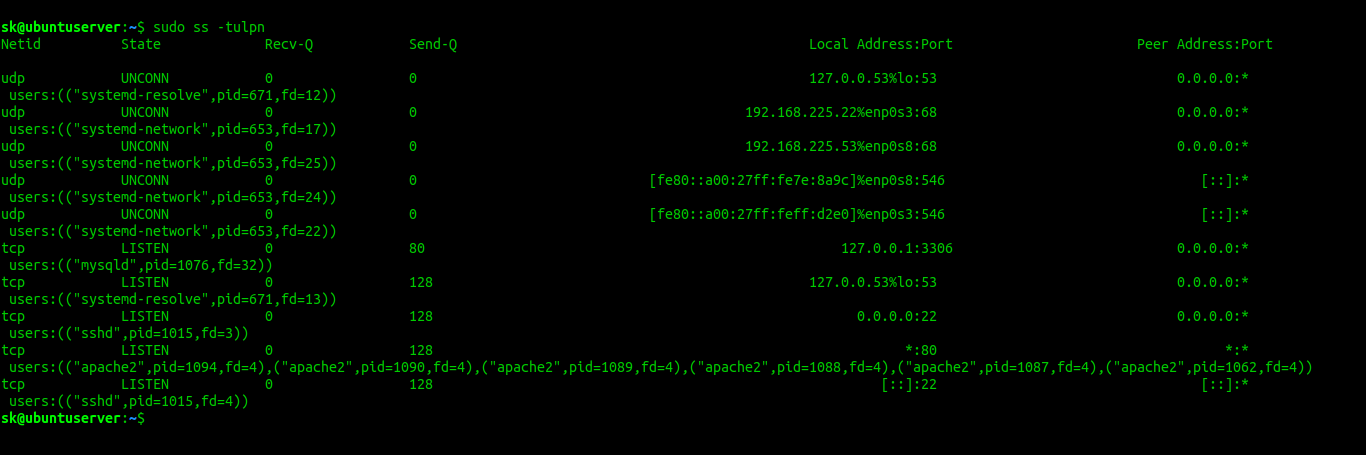
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port
udp UNCONN 0 0 127.0.0.53%lo:53 0.0.0.0:* users:(("systemd-resolve",pid=671,fd=12))
udp UNCONN 0 0 192.168.225.22%enp0s3:68 0.0.0.0:* users:(("systemd-network",pid=653,fd=17))
udp UNCONN 0 0 192.168.225.53%enp0s8:68 0.0.0.0:* users:(("systemd-network",pid=653,fd=25))
udp UNCONN 0 0 [fe80::a00:27ff:fe7e:8a9c]%enp0s8:546 [::]:* users:(("systemd-network",pid=653,fd=24))
udp UNCONN 0 0 [fe80::a00:27ff:feff:d2e0]%enp0s3:546 [::]:* users:(("systemd-network",pid=653,fd=22))
tcp LISTEN 0 80 127.0.0.1:3306 0.0.0.0:* users:(("mysqld",pid=1076,fd=32))
tcp LISTEN 0 128 127.0.0.53%lo:53 0.0.0.0:* users:(("systemd-resolve",pid=671,fd=13))
tcp LISTEN 0 128 0.0.0.0:22 0.0.0.0:* users:(("sshd",pid=1015,fd=3))
tcp LISTEN 0 128 *:80 *:* users:(("apache2",pid=1094,fd=4),("apache2",pid=1090,fd=4),("apache2",pid=1089,fd=4),("apache2",pid=1088,fd=4),("apache2",pid=1087,fd=4),("apache2",pid=1062,fd=4))
tcp LISTEN 0 128 [::]:22 [::]:* users:(("sshd",pid=1015,fd=4))To filter output for a particular service (E.g. mysqld), use:
$ sudo ss -tulpn | grep -w mysqld
tcp LISTEN 0 80 127.0.0.1:3306 0.0.0.0:* users:(("mysqld",pid=1076,fd=32))For more details, refer man pages.
$ man ss
Method 3 - Using lsof
As the name says, lsof is a command line utility to list all open files belonging to all active processes.
To install it on Linux, use the following commands depending the distribution type you use.
On Arch Linux:
$ sudo pacman -S lsof
On Debian, Ubuntu:
$ sudo apt install lsof
On CentOS, RHEL:
$ sudo yum install lsof
On Fedora:
$ sudo dnf install lsof
To find which processes are running on which ports, simply specify the port number as shown in the following command:
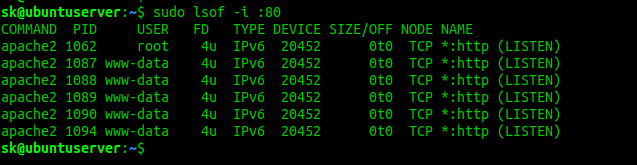
$ sudo lsof -i :80
Sample output:
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME apache2 1062 root 4u IPv6 20452 0t0 TCP *:http (LISTEN) apache2 1087 www-data 4u IPv6 20452 0t0 TCP *:http (LISTEN) apache2 1088 www-data 4u IPv6 20452 0t0 TCP *:http (LISTEN) apache2 1089 www-data 4u IPv6 20452 0t0 TCP *:http (LISTEN) apache2 1090 www-data 4u IPv6 20452 0t0 TCP *:http (LISTEN) apache2 1094 www-data 4u IPv6 20452 0t0 TCP *:http (LISTEN)
For more details, refer man pages.
$ man lsof
Method 4 - Using fuser command
fuser is yet another command line utility to identify processes using files or sockets. It displays the PIDs of processes using the specified files or file systems.
It is also available in the default repositories of most Linux distributions.
To install it on Arch Linux, run:
$ sudo pacman -S psmisc
On Debian, Ubuntu:
$ sudo apt install psmisc
On CentOS, RHEL:
$ sudo yum install psmisc
On Fedora:
$ sudo dnf install psmisc
First we need to find the PID of a service or process listening on a particular port. For example, I am going to find the PID of a process listening on port 3306 using command:
$ sudo fuser 3306/tcp
You will see an output like below.
3306/tcp: 1076
Here, 1076 is the PID.
And then find out the actual process using the PID using command:
$ ps -p 1076 -o comm= mysqld
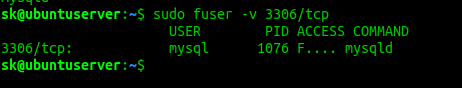
Alternatively, you can use -v flag to view the complete details in a single command.
$ sudo fuser -v 3306/tcp
USER PID ACCESS COMMAND
3306/tcp: mysql 1076 F.... mysqldFor more details, go through the man pages.
$ man fuser
Conclusion
You now know four different tools to find which processes are listening on what ports in Linux. All four of them are easy to use and available in most Linux distributions. If you know any other tools, let us know in the comment section below. I will check and update this list accordingly.
Related Read: