Debian 11, codenamed bullseye, has been released! This step by step guide explains how to upgrade to Debian 11 bullseye from Debian 10 buster from command line.
Debian 11 "bullseye" is released
The long wait is over! Debian 11, codenamed "bullseye", stable version is available for download!!
Thanks to the combined work of the Debian Security team and the Debian Long Term Support team, Debian 11 will be supported for next 5 years.
The new Debian 11 distribution ships with many different desktop environments (DE) and several updated applications.
Debian 11 currently includes the following DEs:
- Gnome 3.38,
- KDE Plasma 5.20,
- LXDE 11,
- LXQt 0.16,
- MATE 1.24,
- Xfce 4.16.
For more details, check the Debian 11 "bullseye" release notes.
If you're prefer fresh Debian 11 installation, check the following guide.
Upgrade to Debian 11 bullseye from Debian 10 buster
Let us check the currently installed Debian version using command:
$ cat /etc/debian_version 10.10
You can also use lsb_release command to display Debian version.
$ lsb_release -a
Sample output:
No LSB modules are available. Distributor ID: Debian Description: Debian GNU/Linux 10 (buster) Release: 10 Codename: buster
As you see in the above output, I am using the latest Debian 10 buster system. Now, let us start to upgrade Debian 10 buster to Debian 11 bullseye.
Step 1 - Update and upgrade all currently installed packages
Before we start upgrade Debian buster to bullseye, make sure you've updated and upgraded all existing packages to their latest available version by running the following commands one by one:
$ sudo apt update
$ sudo apt upgrade
$ sudo apt dist-upgrade
And then clean any leftover packages and configuration files using commands:
$ sudo apt autoremove
$ sudo apt autoclean
$ sudo find /etc -name '.dpkg-' -o -name '.ucf-' -o -name '*.merge-error'
Reboot your system to apply all updates.
$ sudo reboot
Step 2 - Backup your data
The next important step is backup. Make sure you have taken backup of all important personal files, directories and configuration files.
The important things you'll want to back up are the contents of /etc, /var/lib/dpkg, /var/lib/apt/extended_states and the output of dpkg --get-selections "*" (the quotes are important) command.
You can also use any one or two of the following backup applications to backup the data and system settings in your Debian Linux system.
- Rsync - A powerful command line utility to backup personal data and $HOME directory.
- Deja Dup - A simple GUI utility to backup personal data.
- Timeshift - A graphical application to backup system files and settings.
- Restic - A command line utility to save multiple revisions of files and directories in an encrypted repository stored on different backends.
- Rsnapshot - A command line utility to create periodic snapshots of local machines, and remote machines over ssh.
I personally use Deja Dup and Timeshift for backup. You can pick any one or more of your choice from the above list.
Step 3 - Update software repositories
Before updating the software repositories in Debian buster, first backup the current software source list.
$ mkdir ~/apt
$ sudo cp /etc/apt/sources.list ~/apt
$ sudo cp -rv /etc/apt/sources.list.d/ ~/apt
Verify the contents of ~/apt directory to make sure the software repository lists have been copied.
$ ls apt/
sources.list sources.list.d
Now we need to update the current repository list to point to Debian 11 repositories.
To replace and update Debian 10 repositories with Debian 11 repositories, run:
$ sudo sed -i 's/buster/bullseye/g' /etc/apt/sources.list
$ sudo sed -i 's/buster/bullseye/g' /etc/apt/sources.list.d/*
Now verify if the sources list file is updated with new repository links:
$ cat /etc/apt/sources.list
Sample output:
deb http://deb.debian.org/debian/ bullseye main deb-src http://deb.debian.org/debian/ bullseye main deb http://security.debian.org/debian-security bullseye/updates main deb-src http://security.debian.org/debian-security bullseye/updates main # bullseye-updates, previously known as 'volatile' deb http://deb.debian.org/debian/ bullseye-updates main deb-src http://deb.debian.org/debian/ bullseye-updates main # This system was installed using small removable media # (e.g. netinst, live or single CD). The matching "deb cdrom" # entries were disabled at the end of the installation process. # For information about how to configure apt package sources, # see the sources.list(5) manual.
Heads Up: For Debian bullseye, the security suite is now named bullseye-security instead of codename/updates and users should adapt their APT source-list files accordingly when upgrading.
So we need to update the security lines in the APT configuration file.
Find the following lines in your sources.list file:
deb http://security.debian.org/debian-security bullseye/updates main deb-src http://security.debian.org/debian-security bullseye/updates main
And replace them with following lines:
deb https://deb.debian.org/debian-security bullseye-security main contrib deb-src https://deb.debian.org/debian-security bullseye-security main contrib
After changing the security lines, the final APT sources.list file should look like below:
deb http://deb.debian.org/debian/ bullseye main deb-src http://deb.debian.org/debian/ bullseye main deb https://deb.debian.org/debian-security bullseye-security main contrib deb-src https://deb.debian.org/debian-security bullseye-security main contrib # bullseye-updates, previously known as 'volatile' deb http://deb.debian.org/debian/ bullseye-updates main deb-src http://deb.debian.org/debian/ bullseye-updates main # This system was installed using small removable media # (e.g. netinst, live or single CD). The matching "deb cdrom" # entries were disabled at the end of the installation process. # For information about how to configure apt package sources, # see the sources.list(5) manual.
As you see in the above output, the sources.list file is updated with new Debian 11 repository links. Save the file and exit.
Update the repository lists using command:
$ sudo apt update
Step 4 - Perform minimal system upgrade
In some cases, doing a full system upgrade (which is explained in the next step) will remove large number of packages that you want to keep. So Debian developers recommends two-part upgrade process, namely minimal upgrade and full upgrade.
The minimal upgrade will upgrade all existing packages without installing or removing any other packages.
First, you need to do minimal upgrade using command:
$ sudo apt upgrade --without-new-pkgs
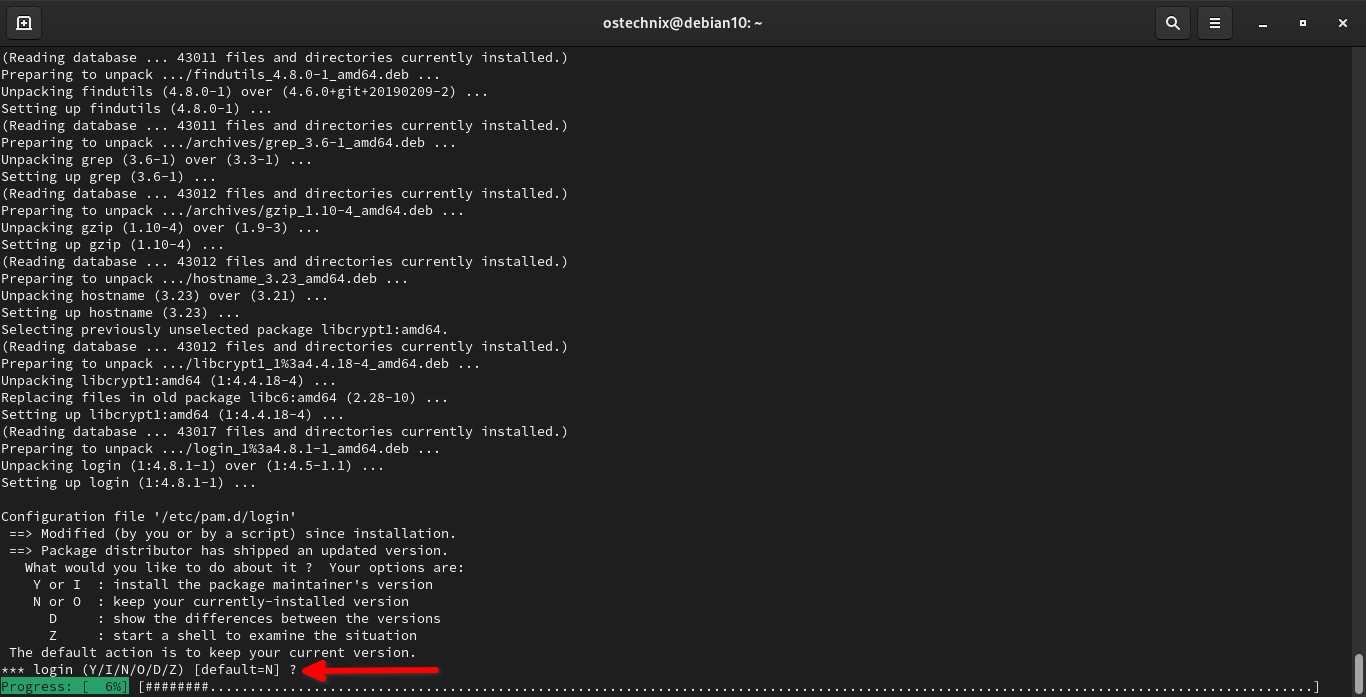
Keep an eye on the screen. During the upgrade process, you'll be asked to answer a few questions like what do you want to do with a configuration file or if you want to restart a service etc. The questions may vary depending upon the number of installed packages in your current Debian system.
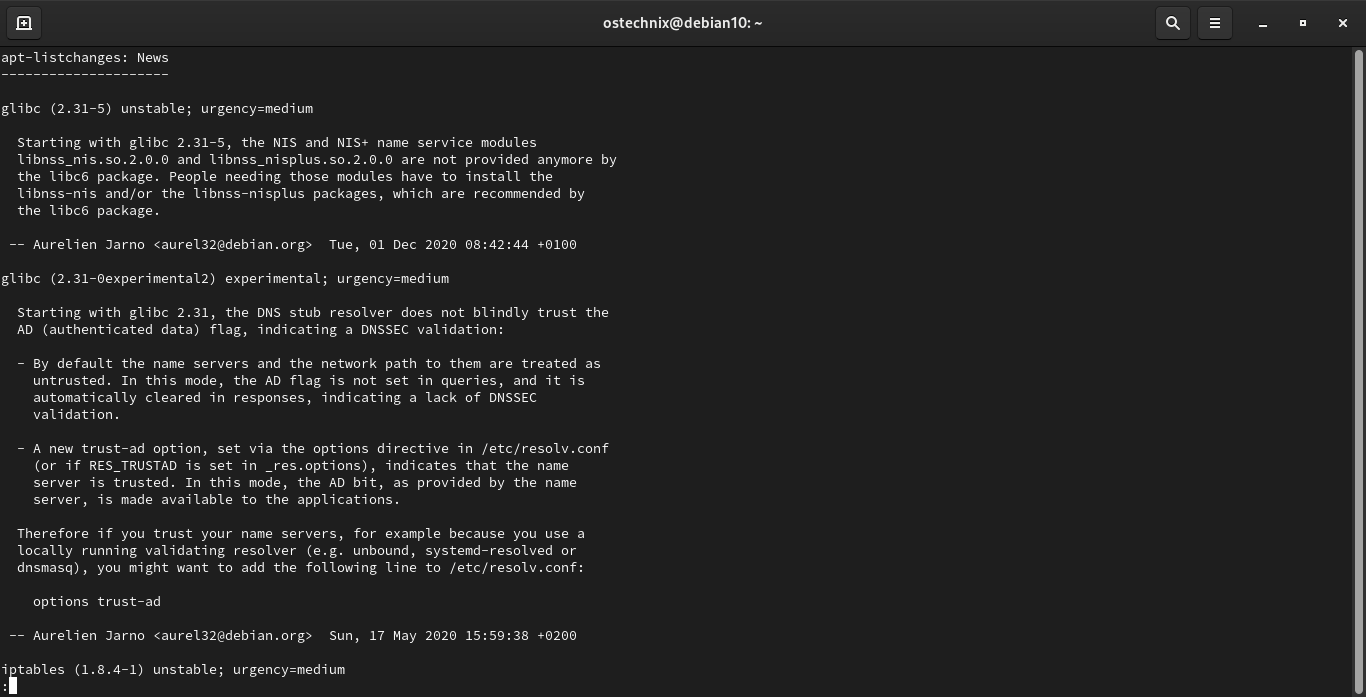
If the apt-listchanges package is installed, it will show important information about upgraded packages in a pager after downloading the packages. Press ENTER to read the information or simply press q to exit and return back to the upgrade process.
Next you will be asked what do you want to do with a specific configuration file ( E.g. pam login file). Read the instructions on the screen and decide accordingly. If you're not sure what to do, just go with defaults by simply pressing ENTER key:
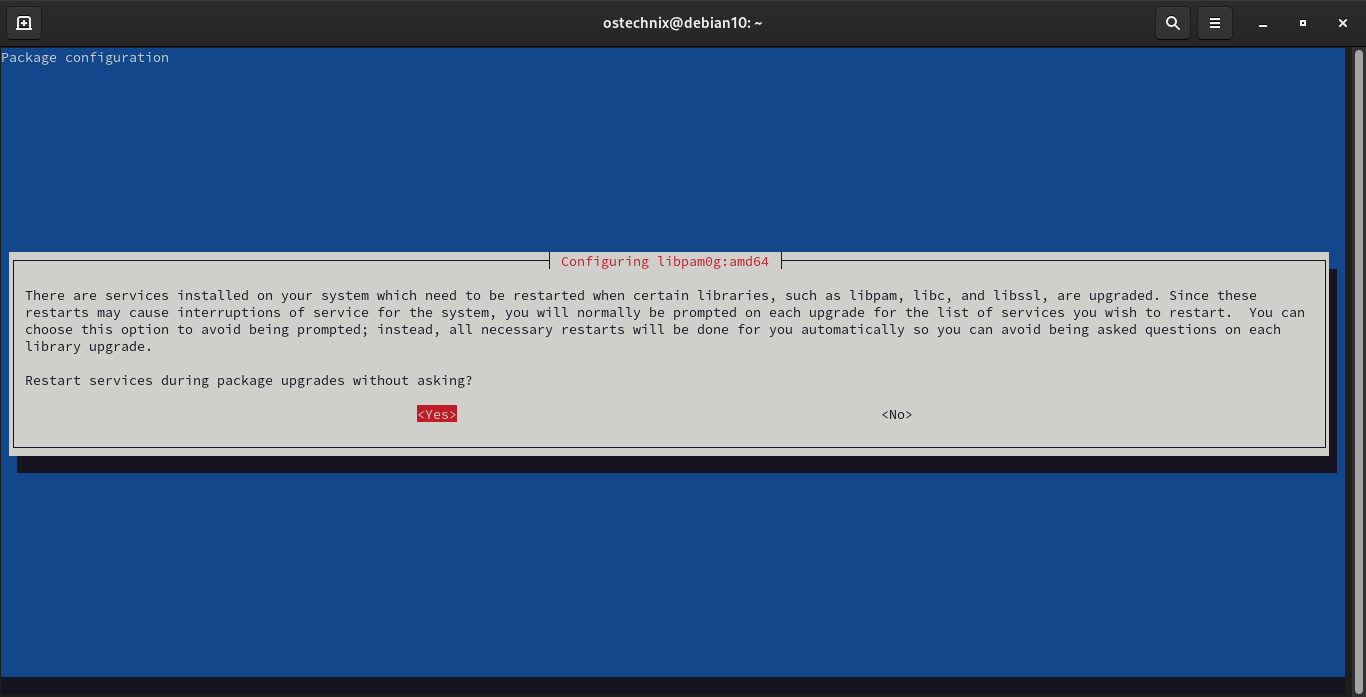
Many services installed on your Debian system need to be restarted when certain libraries, such as libpam, libc, and libssl, are upgraded. Since these restarts may cause interruptions of service for the system, you will normally be prompted on each upgrade for the list of services you wish to restart. If you want to avoid being asked such questions on each library upgrade choose Yes and press ENTER to continue.
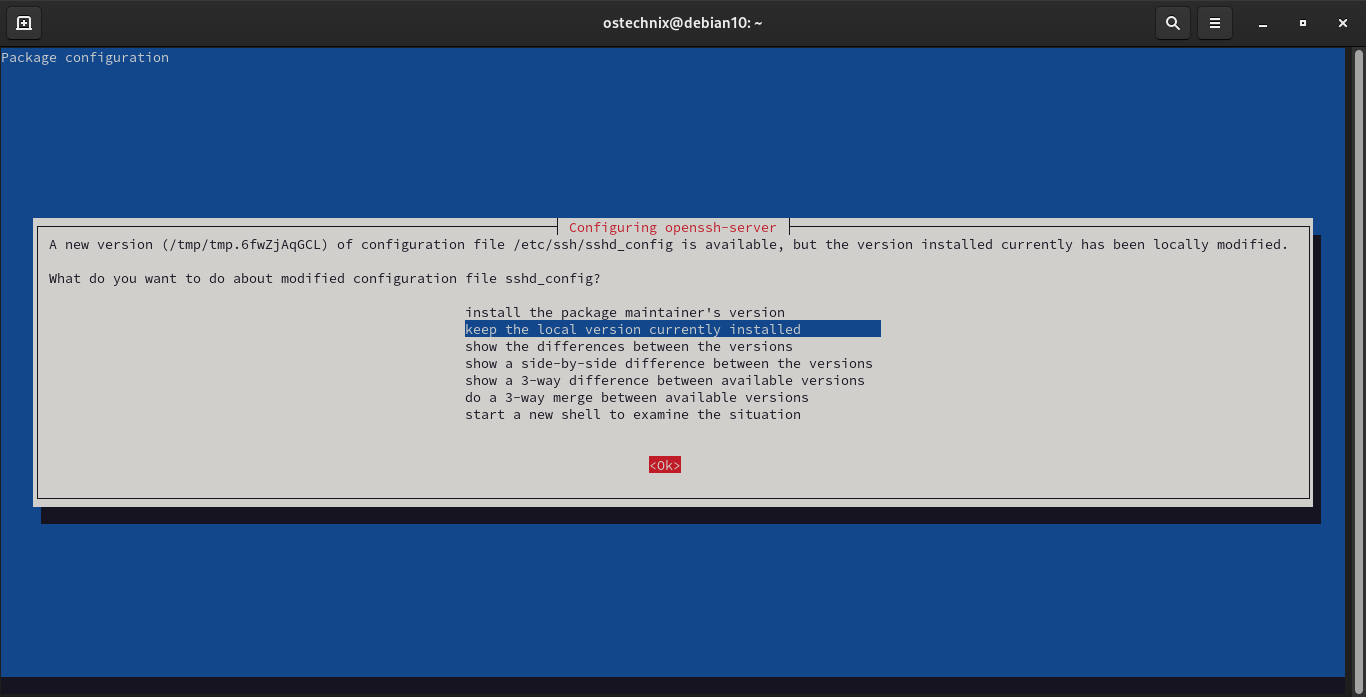
Next the installer will prompt what do you want to do about modified configuration file sshd_config. Select any one of the given choices and choose OK and press ENTER to continue.
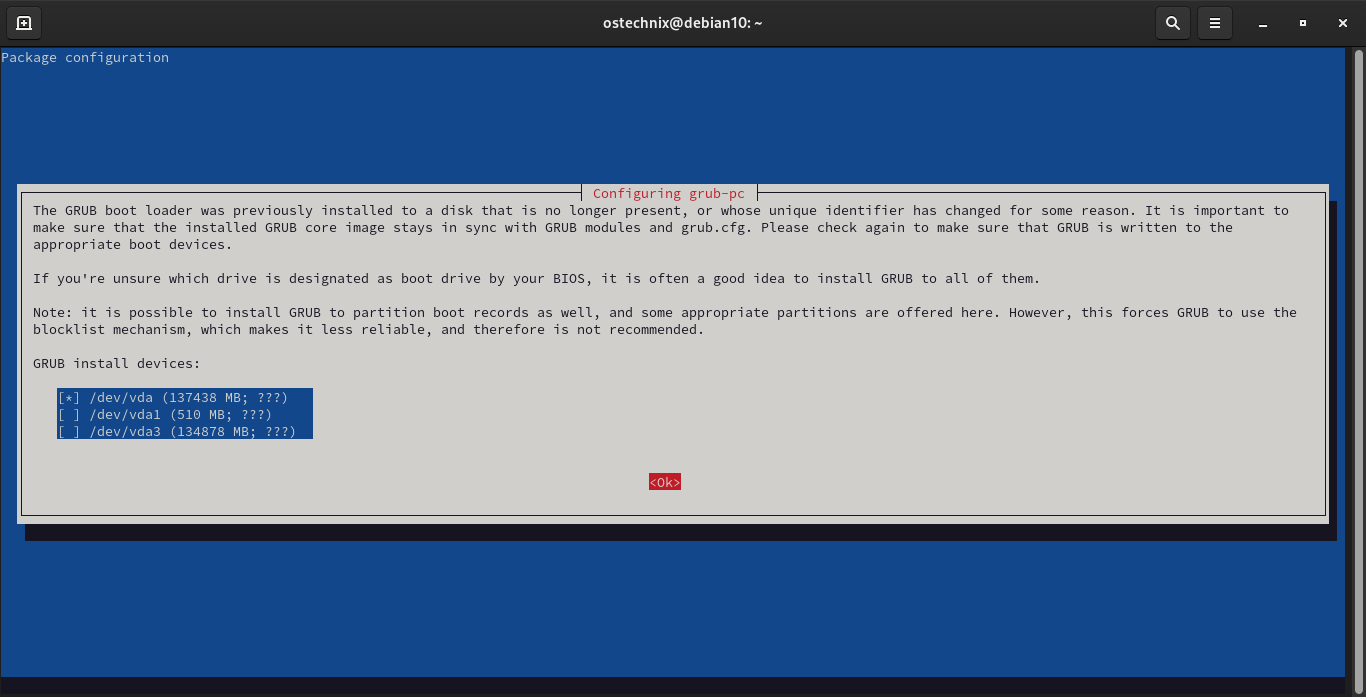
Choose where do you want to install Grub and select OK and press ENTER key to continue.
The minimal upgrade process will complete in a few minutes.
Step 5 - Upgrade to Debian 11 bullseye
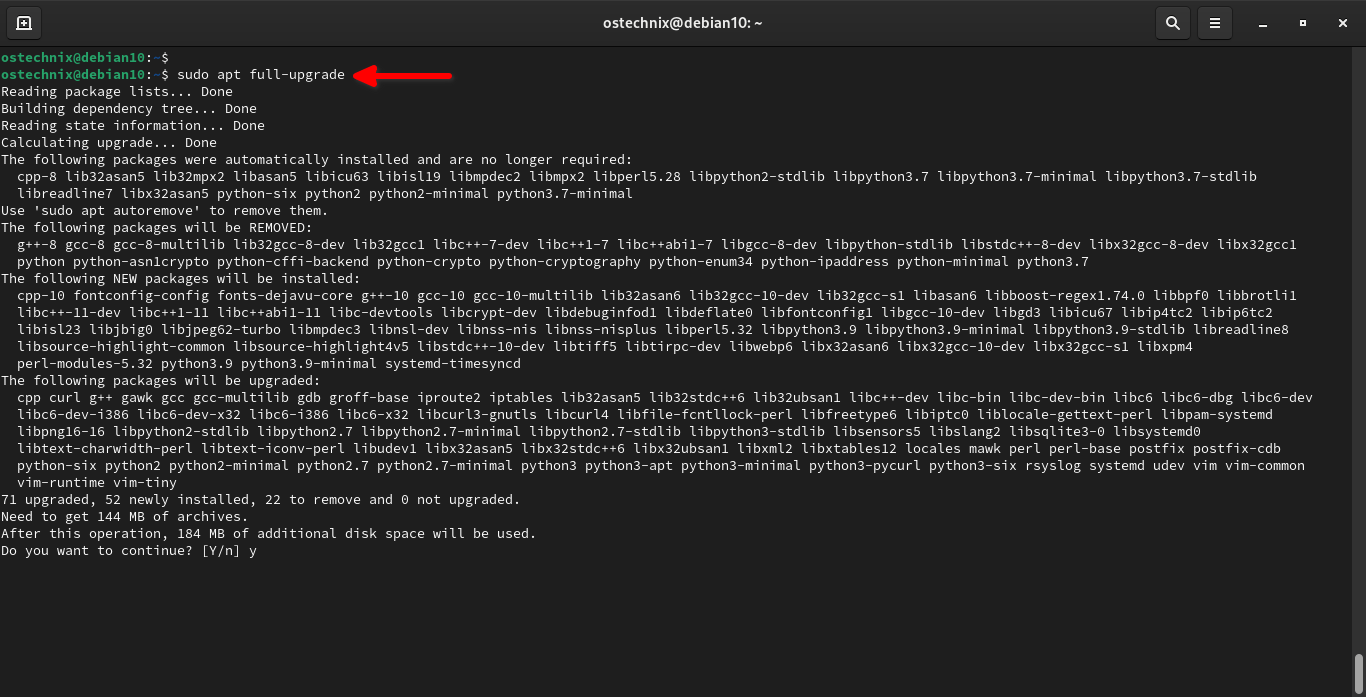
Now start the actual Debian 11 bullseye upgrade using command:
$ sudo apt full-upgrade
Again, you need to keep an eye on the screen and answer all questions that might come up as usual.
As stated earlier, if the apt-listchanges package is installed, it will show important information about upgraded packages in a pager after downloading the packages. Press q to quit after reading the information and continue upgrade.
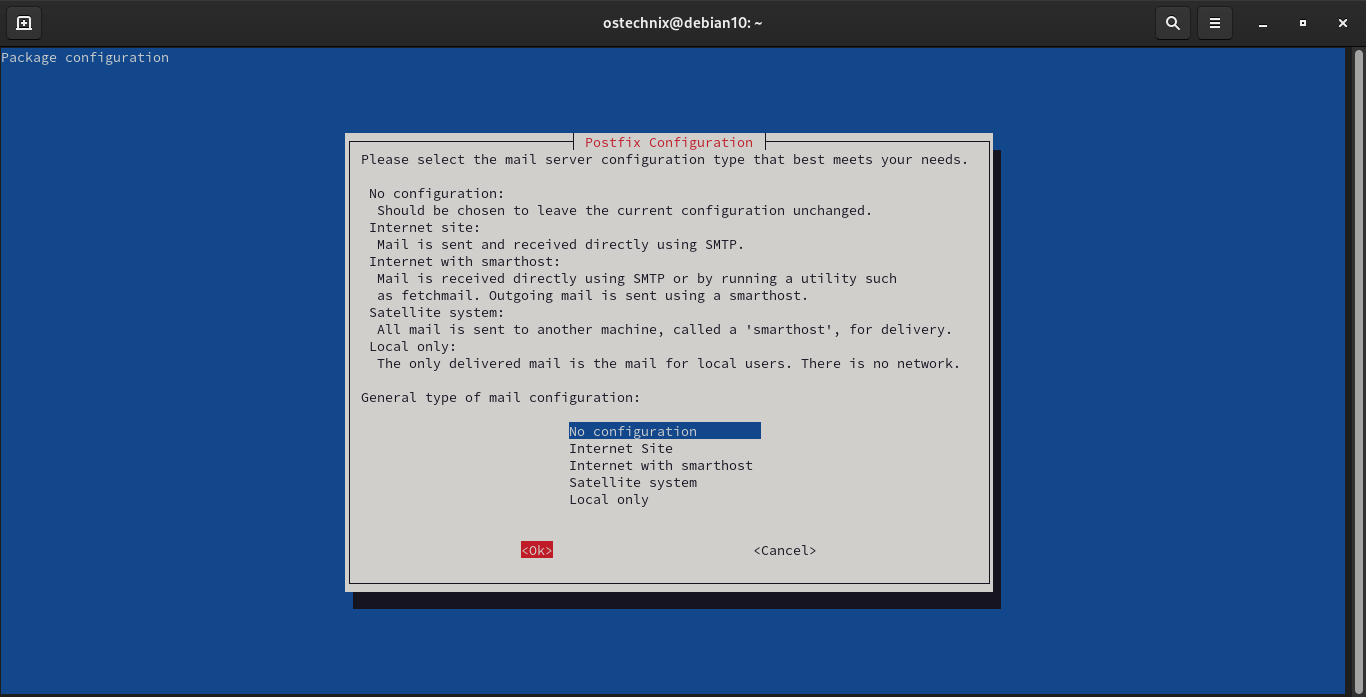
Select the mail server configuration type from the list, and choose Ok and press ENTER to continue:
Once the Debian 11 upgrade process is completed, reboot your system:
$ sudo reboot
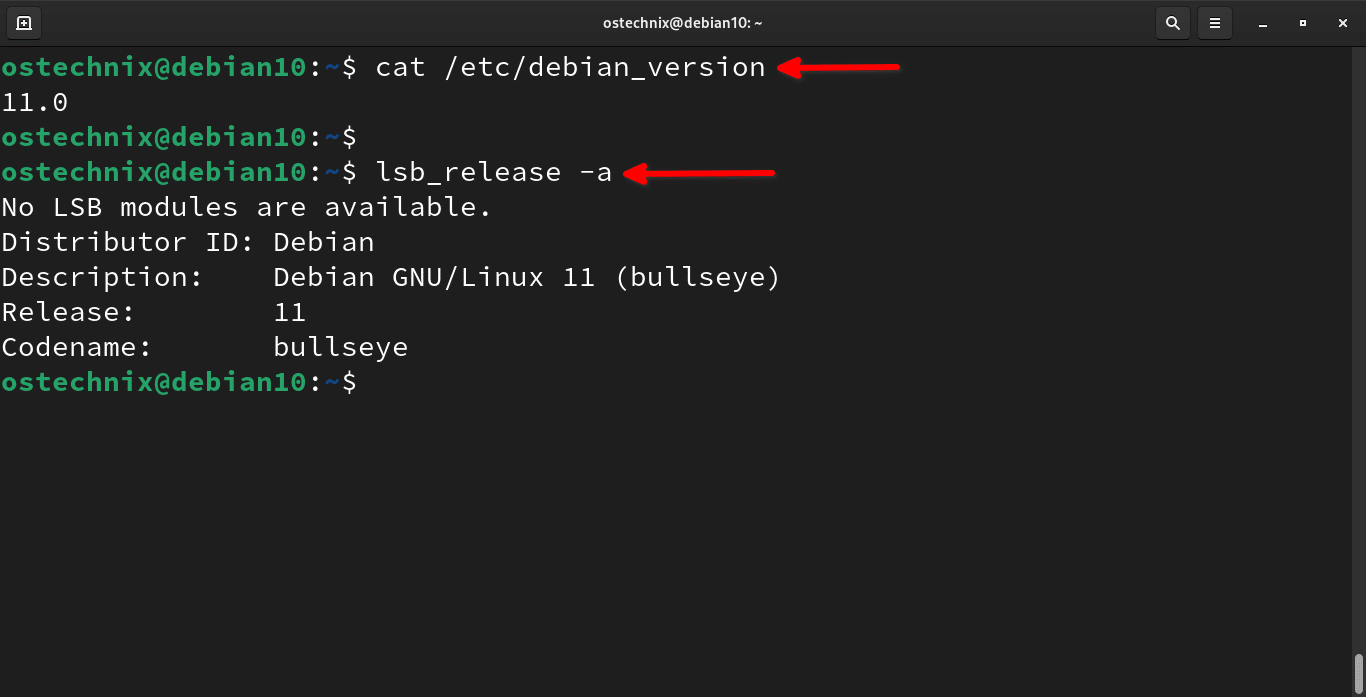
Log in to the system and Check Debian 11 bullseye version using command:
$ cat /etc/debian_version 11.0
Or, use lsb_release command:
$ lsb_release -a
Sample output:
No LSB modules are available. Distributor ID: Debian Description: Debian GNU/Linux 11 (bullseye) Release: 11 Codename: bullseye
Congratulations! We have successfully upgraded Debian 10 buster to Debian 11 bullseye.
Optionally, you can remove all packages that are no longer required using commands:
$ sudo apt --purge autoremove
$ sudo apt autoclean
Step 6 - Verify if everything works fine
Log in to your newly upgraded Debian 11 system and check everything works fine. You may need to open and/or run a few installed applications and verify if they are working as usual. If something breaks your system, please let us know in the comment section or reach out to your Debian forum.
Debian 11 is just released (August 14, 2021), so you may expect some minor glitches. But in my case, the upgrade process was smooth and everything worked just fine.
Step 7 - Restore the backup
Once everything works as expected, restore the backup which you've taken before upgrading your system.
Install new applications of your choice and start using Debian 11 bullseye edition!
TL;DR (TOO LONG DIDN'T READ)
Basically, Debian 11 bullseye upgrade process consists of the following steps:
- Update all existing packages
sudo apt updatesudo apt upgrade
- Restart system
sudo reboot
- Backup important data
- Update software repositories
sudo sed -i 's/buster/bullseye/g' /etc/apt/sources.listsudo sed -i 's/buster/bullseye/g' /etc/apt/sources.list.d/*
- Perform minimal upgrade
sudo apt upgrade --without-new-pkgs
- Upgrade to Debian 11 bullseye
sudo apt full-upgrade
- Restart system
sudo reboot
Hope this helps.
Resource:



20 comments
Very useful guide..!
Glad you found it useful. Happy to help.
Thanks for the writeup.
Is it intentional to restore the backup anyways in last step? Just making sure.. if everything works, it shouldn’t delete any important files, or does it?
Yes, if the upgrade was smooth and error-free, there is no need to restore the data.
Very useful, just an issue in sourcelist:
when I run “apt update” I get an error that says something not found for debian-security.
I solved with the help of this entry:
https://www.debian.org/releases/bullseye/amd64/release-notes/ch-information#security-archive
thanks
You have an error in step 3.
For APT source lines referencing the security archive, the format has changed slightly along with the release name, going from buster/updates to bullseye-security.
https://www.debian.org/releases/bullseye/amd64/release-notes/ch-information.en.html#security-archive
Thanks for the heads up. I have updated the guide now.
You made a big job. Unfortunately after doing all as you said, my system booting with the new kernel can’t load it, so I have to reboot the pc and select the old kernel (4.19 from buster). Other error is about the graphic device: again can’t load it…I’m trying to fix them , but looks hard to do. Some idea?
My Debian 10 setup is minimal, so I haven’t had any issues while upgrading. Also check the following official documentation. This page lists the issues to be aware of for bullseye.
https://www.debian.org/releases/stable/amd64/release-notes/ch-information.en.html
I have seen the link but it doesn’t write about errors on the kernel during boot; the 5.0 can’t load so I have to go back to the 4.19 during boot. System looks changed (now is bullseye) but the kernel is again from Buster. Other problems: NVidia Persistence Daemon can’t load (why?); cgroups: memory recursive prot. So the system loads till check of network and stops there… why, if I have everything ok and was ok during install?
I guess NVIDIA was the culprit. Generally, Nvidia doesn’t work well with Linux. May be you should wait for couple days and then upgrade to bullseye.
I would add something to stress how important this part is and explain why it’s absolutely necessary:
sudo apt upgrade --without-new-pkgsI was breezing along and forgot the –without-new-pkgs flag and it broke all kinds of stuff. I ended up having to remove aptitude, which removed gnome, gdm3, etc. So, I had to boot into recovery mode and fix a bunch of stuff. Many hours later, I got everything back to normal, but it was all because of a stupid flag.
We all make mistakes. Glad you fixed it yourself.
lost ability to use deb at beginning of a command, so had to add contrib non-free to that Debian line. I followed another site’s directions to fix that:
sudo apt-get install software-properties-common
then,
sudo add-apt-repository “deb http://http.debian.org/debian/ bullseye main contrib non-free”. Because of that, I was a bit afraid to add those wsecurity lines – exhausted, really. This upgrade took a long time on my PC that already ran really slow (chip bug, I think).
Sorry to hear about that. I didn’t add contrib repository. My upgrade was smooth.
Excellent guide. I have been running Debian for years and always follow a guide like yours for reassurance, even though I should know what I’m doing by now.
This is the best one I’ve used. Thank you.
Happy to help. Thank you for your positive feedback.
Thanks. This was an excellent guide. There are a lot of 1/2 hearted efforts “out there” so finding a solid document is gold.
It’s a 3rd-party package issue, but just a note that I had to manually reinstall Virtualbox after this process. Not sure why Virtualbox got wiped in the upgrade process, but no big deal as an “apt install virtualbox-6.1” was all that was needed (I had all the /etc/apt/ config and gpg keys in place from the previous install).
So thanks again for a very solid doc.
Exellent! thanks for the hardwork and the guide it helped a lot.
We also have a upgrade description there: https://dietpi.com/blog/?p=811.
Possibly some of the additional information given there could help in case of some problems.